Logins and sessions
Successful and failed authentication attempts, session starts and ends, with originating IP.
Vauzy captures a complete trail of activity, from logins to edits and credential access. You can always see who did what, when it happened, and from which IP. Clear, tamper-resistant evidence you can trust.
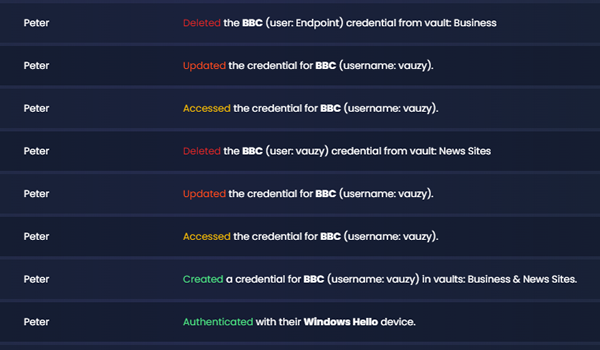
From login to updating credentials and accessing them. One continuous record that’s easy to scan and filter.
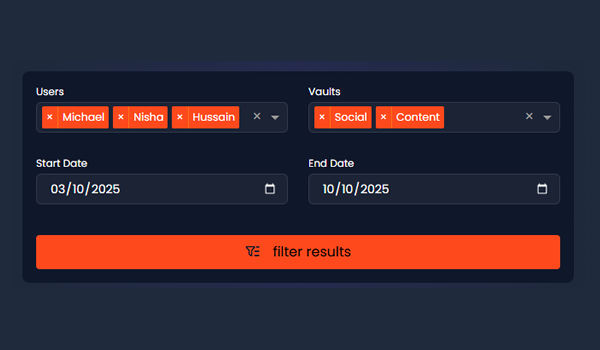
Search by user, action, vault, credential, date range, or IP to get answers fast.
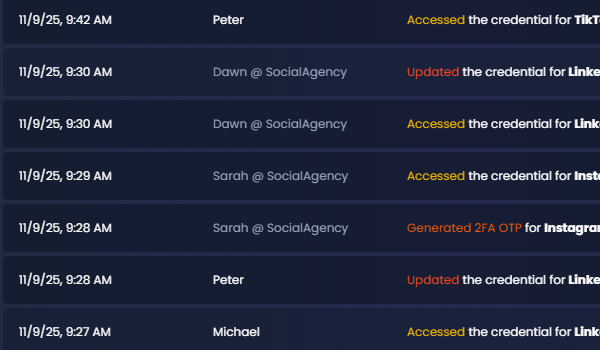
Clients see agency actions, agencies see client activity. Client names are obscured for agencies to protect privacy.
Successful and failed authentication attempts, session starts and ends, with originating IP.
Credential and vault changes, including permission updates, recorded with actor, timestamp, and IP.
Who viewed or used a credential, when they accessed it, and from which IP, across shared vaults.
Vault and credential share events, invite accepts, and role changes, all tracked for accountability.
Changes to vault access and organisation settings, captured with full context.
Generate shareable summaries to show activity and compliance progress without exposing sensitive values.
Record
Every action is captured in real time with actor, action, timestamp, and IP.
Review
Filter by user, vault, credential, or severity. Surface anomalies and unusual access patterns instantly.
Report
Share summaries with stakeholders or clients. Build trust with clear evidence and a consistent trail.
Audit logs are visible to both sides. Clients see which agency users acted. Agencies see client activity with client names obscured. Logs include IP addresses, not device data. GDPR-aligned by design.
Yes. We record authentication events, creation, updating, deletion, sharing, and accessing of credentials. Each entry includes the actor, timestamp, and originating IP.
Both sides have visibility in shared contexts. Clients see agency user actions. Agencies can review client activity with privacy safeguards that obscure client names.
We capture IP addresses for context. Device information is not collected at this time.
Yes. Create time-bounded exports and shareable summaries that exclude sensitive values while preserving the evidence you need.
Show exactly how access was handled, by whom, and when. Confidence built on evidence.