Traditional methods
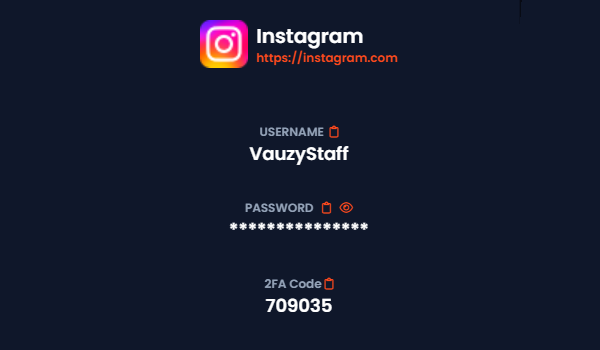
- Requires manual back-and-forth every time a login or 2FA is needed
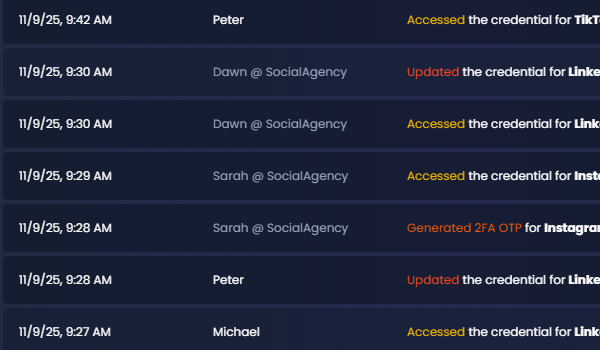
- No audit trail or record of who saw or used the code
- Codes or passwords often expire or leak in screenshots and messages
- No access boundaries
- High risk of reuse, drift and misuse
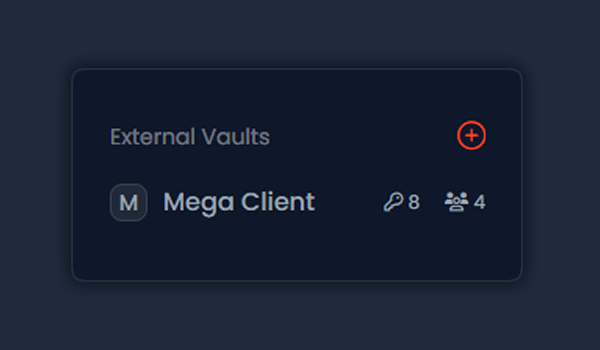
- Have to manage 3rd party users and their access